Think Like the Adversary
A government critical infrastructure unit leveraged CAI to simulate advanced persistent threats using MITRE ATT&CK techniques. By validating detection gaps, testing evasions, and measuring response readiness, the organization strengthened its defensive posture against nation-state adversaries.

Advanced Threat Actor Simulation
CLIENT PROFILE
Critical Infrastructure Defense Unit
High-value target | Nation-state threat exposure | Zero-tolerance security posture
THE CHALLENGE
Are We Ready for APTs?
The organization faced sophisticated adversaries using advanced techniques. Traditional security controls were designed for common attacks, not nation-state tactics. They needed to validate defenses against real APT techniques before facing them in the wild.
- Unknown effectiveness against advanced persistent threats
- Security stack untested against in-memory attacks, evasion techniques
- No way to measure detection and response capabilities
- Compliance requirements for threat simulation
THE SOLUTION
MITRE ATT&CK in Action
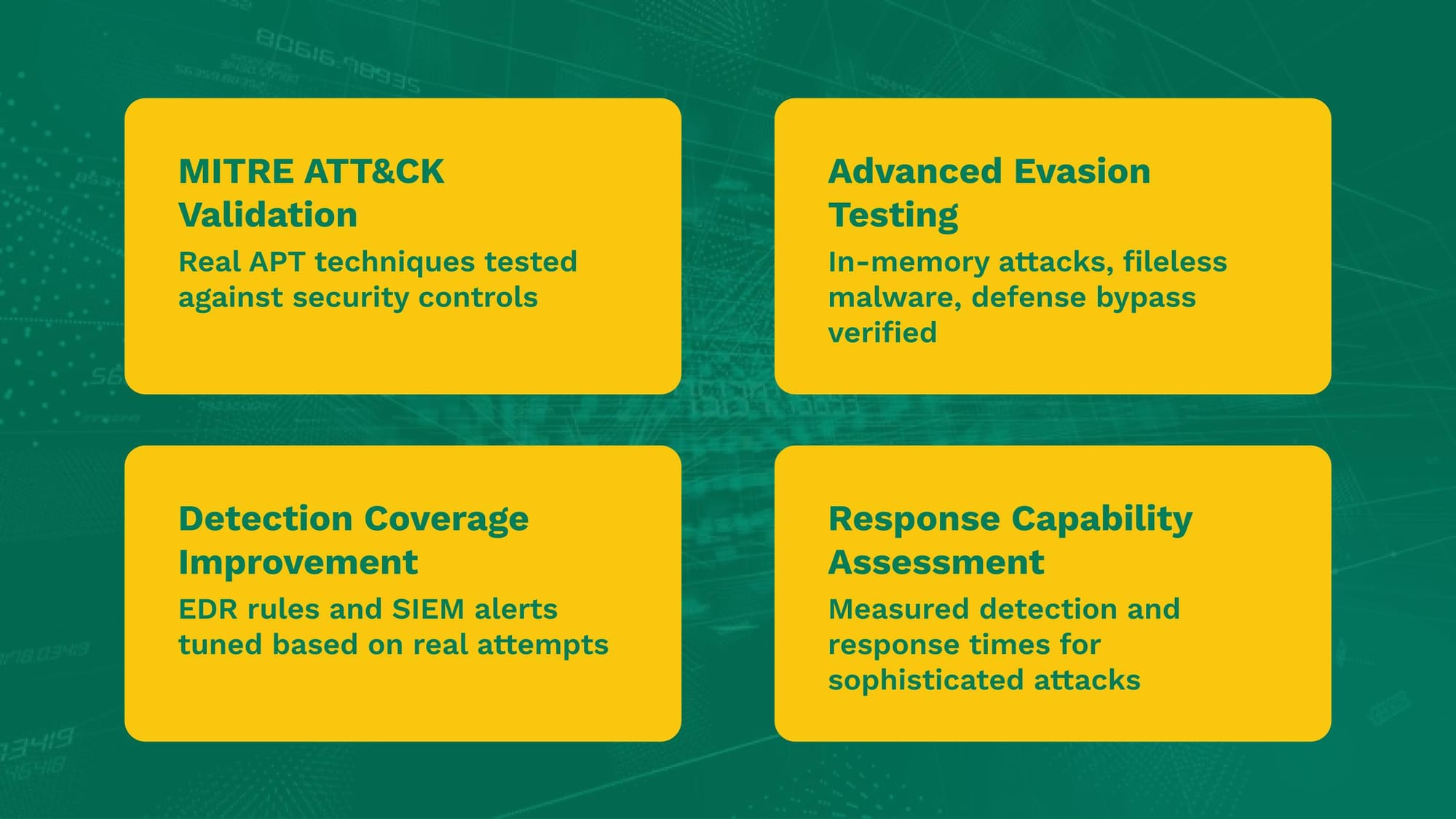
CAI deployed modular attack simulations based on real APT group tactics from the MITRE ATT&CK framework. The platform executed sophisticated techniques—credential dumping, fileless malware, defense evasion—to stress-test detection and response capabilities.
- APT technique simulation mapped to MITRE ATT&CK
- In-memory execution and anti-AV evasion tests
- Credential theft and hash extraction validation
- Detection gap analysis and response time measurement
THE RESULTS
Detection Gaps Closed
IMPACT
Security operations moved from reactive to proactive.
EDR rules were tuned based on real evasion attempts, SIEM alerts were refined, and incident response playbooks were tested against actual attack techniques. The organization gained measurable confidence against nation-state threats.
Want to explore what in-house, autonomous security looks like in practice?
Get started with CAI.
Explore how these research insights translate into practical, scalable security with CAI — and join the conversation by following us on LinkedIn and X, or collaborating with the community on our Discord server.