Penetration Testing Humanoid Social Robots: SoftBank Robotics Case Study
A penetration testing case study on the Pepper and NAO humanoid robots of Softbank Robotics. Security threats identified in social robots used in healthcare and service environments.

This study presents a short sneak peek into the penetration testing activity that we conducted on Pepper and NAO robots from Softbank Robotics. Following a security research approach, our team identified security threats and provided guidance to customers on how to address security issues and mitigate them on these robots. Developed in the context of a commercial application, this robotic case study takes place in an arbitrary service-oriented setting, characterized by an environment where the robot collaborates and works together with human professionals serving customers.
While several flaws apply to both robots, our short recap in here focuses heavily on Pepper, a semi-humanoid robot designed with the ability to detect emotion analyzing expressions and voice tones. The robot's head has four microphones, two HD cameras (in the mouth and forehead), and a 3D depth sensor (behind the eyes). There is a gyroscope in the torso and touch sensors in the head and hands. The mobile base has two sonars, six lasers, three bumper sensors, and a gyroscope.
Pepper is designed to be highly interactive, however, cyber security has barely been considered in its development. This fact became evident from our research, which complements previous work and raises additional concerns. Thanks to the permission for disclosure, we hereby leave a partial report of our findings and ultimately encourage end-users to carefully consider the privacy of their customers when they are exposed to these insecure robots.
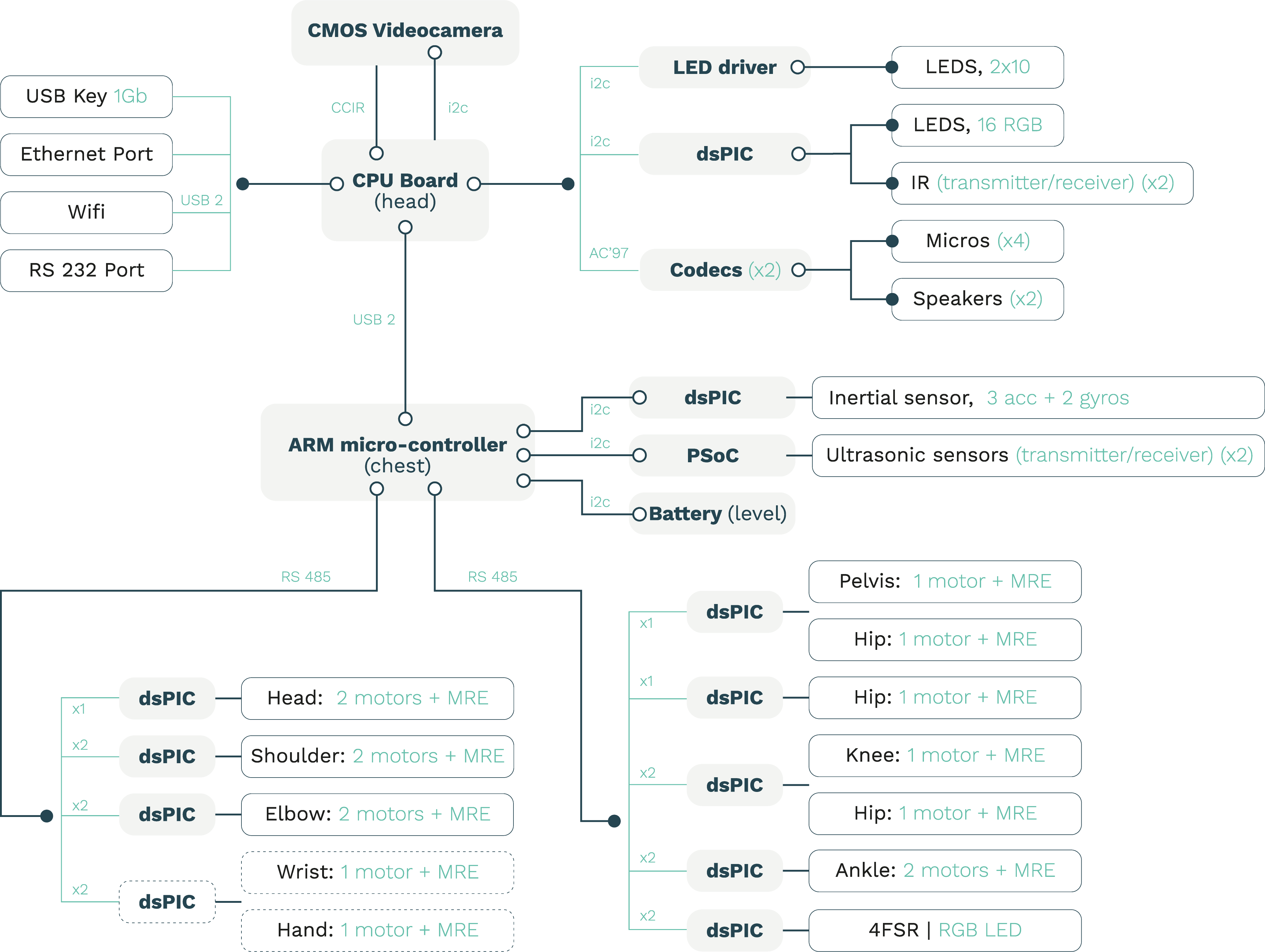
ROBOT HARDWARE COMPONENTS
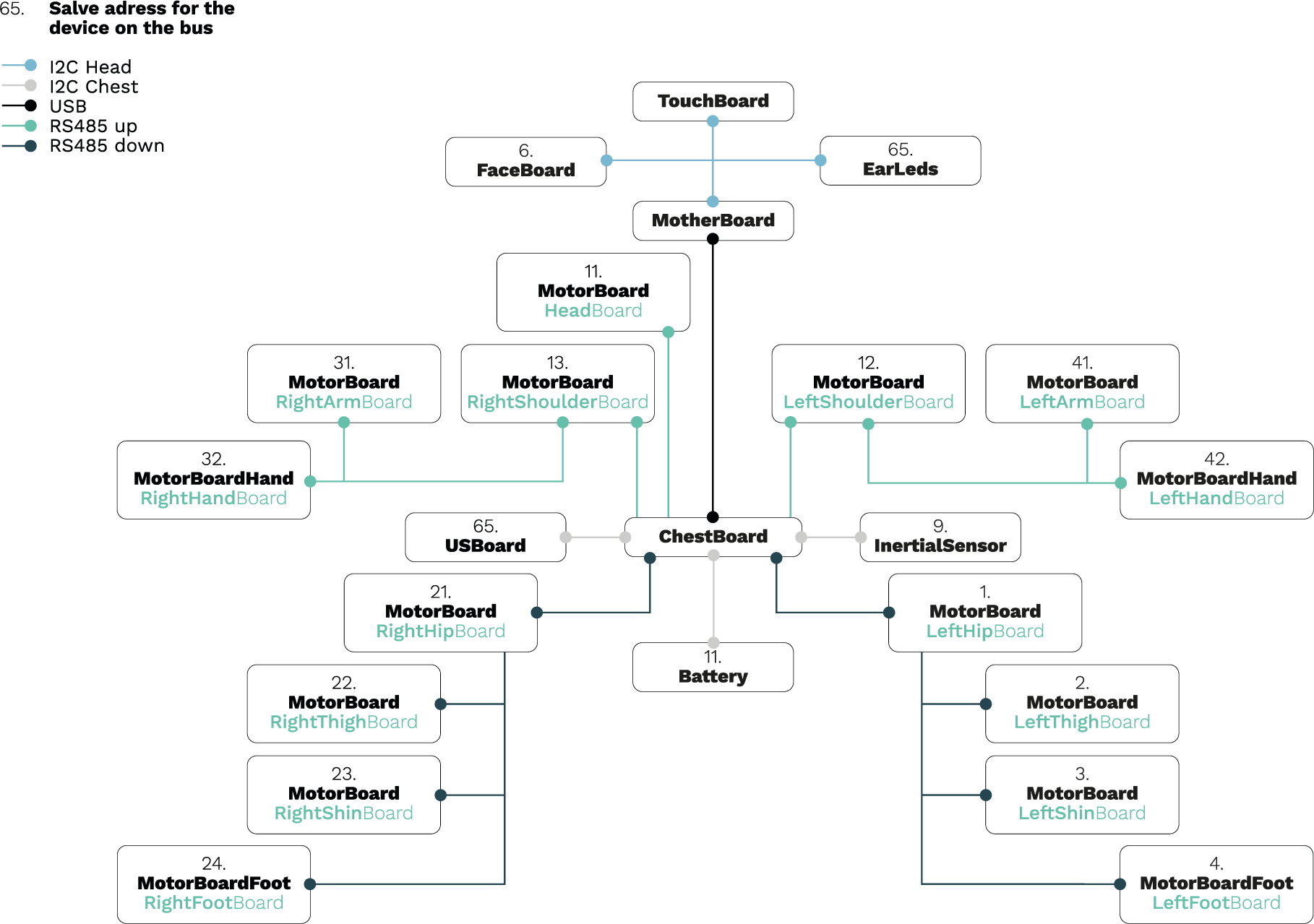
LOW LEVEL ARCHITECTURE
ACTORS
- Robotics user
- Robotics operator
- Robotics researcher
- Vendor upon delivery
- Bad actor
THREATS, VULNERABILITIES AND MORE
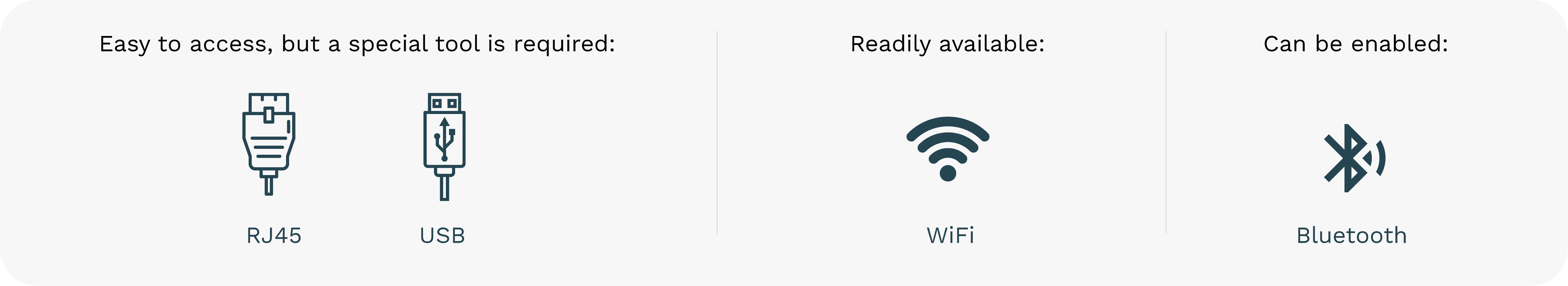
Entry Points
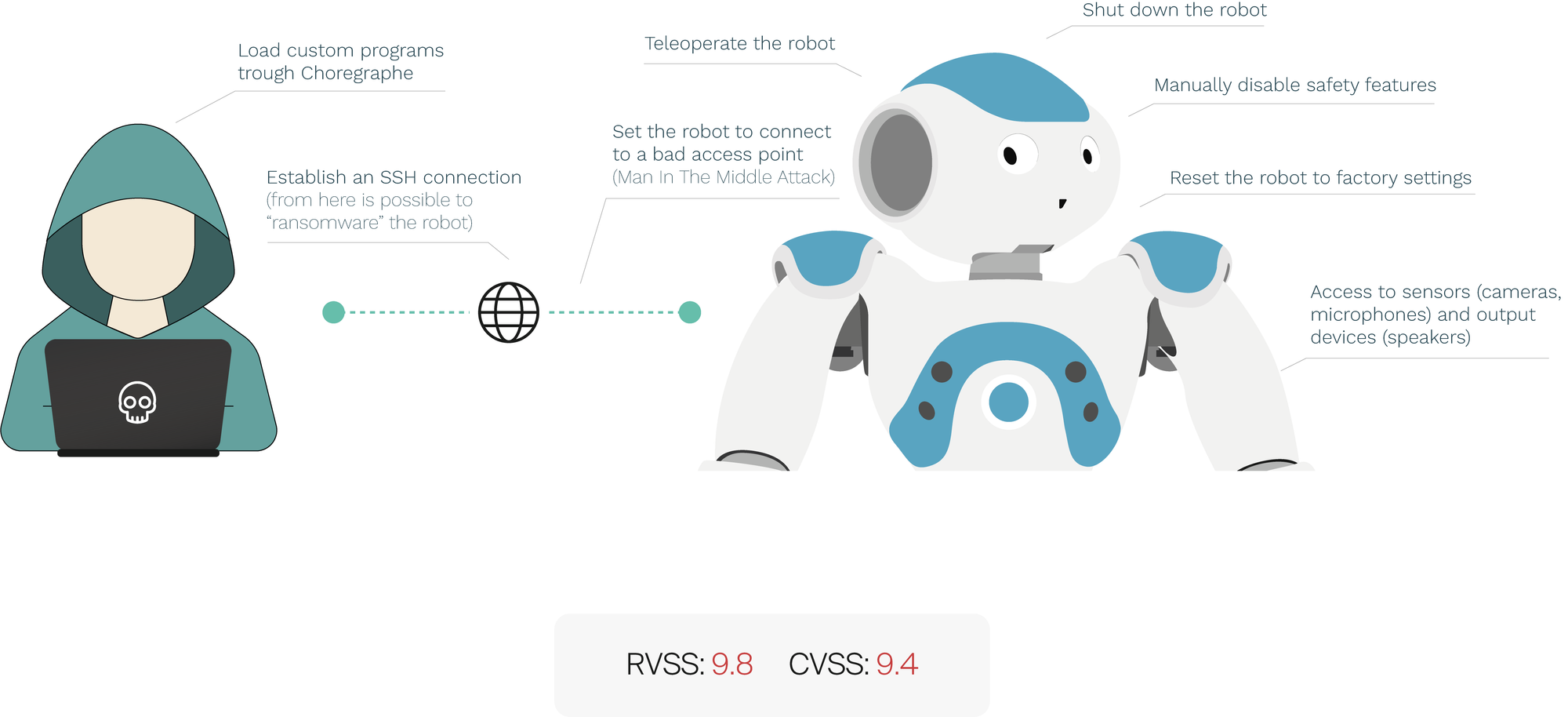
Overview of a potential attack
1. Gain access to the network
Either by social or technical means the bad actor gains access to the network. One of the easiest methods involves using WPS. A feature is available in many commercial access points that is usually enabled by default by the ISPs. The footprinting of this is trivial since it is usually announced alongside the SSID of the network on a mobile device. Pixiedust is used to brute force the WPS PIN and gain access to the network.
2. Scan the network
If you have physical access to the robot you can go ahead and ask it for their IP address -- the robot will happily oblige. Within the network either typing the IP or nao.local into a web browser will take you to the Web interface. In this case NMAP is used to scan the whole network and get the IP address and services of the robot.
3. Gain access to the robot
From here we only need to gain access via SSH since the SSH password and web server is the same. Hydra used with a custom wordlist loaded to perform a dictionary attack. Both the reconnaissance phase (NMAP) and the exploit phase (Hydra) can be combined and be left unattended with a tool like Sparta, further enhancing a covert attack.
THREATS
As previously discussed, strong authentication methods and proper access control should be paramount in social robots. From the high risk to intimacy and information breach from a robot like NAO, to the human and material threats a robot like Pepper poses.
Standing at 120cm tall (4 ft) and equipped with functional human-like hands and arms, cameras and microphones, a rogue robot like Pepper can be able to:
- Steal passwords/credit card information
- Open and close doors
- Activate fire alarms
- Push buttons, turn dials, etc.
- Turn on and off machines
- Carry small objects
- Generate floorplans via SLAM
- Spy on conversations
- Record video and pictures
- Manipulate light tools such as knives/scalpels
We feel this is troubling in any setting but especially around children, elders and in healthcare environments in which a robot like Pepper that is equipped with human-like hands is able to some degree to operate tools intended for humans.
RVD#537 - Hard coded username makes Pepper and NAO susceptible to a Brute force attack
DESCRIPTION
The Default User (NAO) for the robot has a wide array of privileges including SSH access and configuration via browser. Even though the user is prompted to change the password on first use, the user cannot be modified and there is no strength requirements for the password making it more vulnerable to a brute force attack. More so the default Credentials to the robot are publicly available on the user manual.
If not secured properly a bad actor within the same network as Pepper/NAO can gain full access to the robot.
RVD#9 - Improper authorization mechanism in SoftBank's Pepper and NAO robots
DESCRIPTION
Improper authorization mechanism in SoftBank's Pepper and NAO robots could allow remote attackers to gain unrestricted access to robot configuration and sensor data via an unsecured object proxy mechanism.
SEVERITY SCORE: RVSS: 8.2 | CVSS: 9.4
RVD#12 - Authentication bypass in SoftBank's Pepper and NAO robots' web console
DESCRIPTION
An authentication bypass vulnerability in SoftBank's Pepper and NAO robots' web console could allow remote attackers to gain access to restricted resources and alter settings via web browser request tampering. Affects all versions.
SEVERITY SCORE: RVSS: 7.9 | CVSS: 8.8
RVD#14 - Insecure transport in SoftBank's Pepper and NAO robot's Qi Protocol
DESCRIPTION
Insecure transport in SoftBank's Pepper and NAO robot's Qi Protocol could allow man-in-the-middle attackers to eavesdrop sensitive information or affect integrity of sent data. Affects all versions.
SEVERITY SCORE: RVSS: 7.5 | CVSS: 8.6

CONCLUSIONS
We truly believe that a robot like Pepper can be an invaluable tool to help society however in order to do so effectively and without putting humans and environments at risk, we first encourage mitigation of the many and already publicly known security issues present. As of 2018, more than 12,000 Pepper robots were sold in Europe alone. We discourage the use of this robot "as is" and proactively recommend a careful security assessment of applications involving such robots.