Zero-Day Resilience: Scaling Offensive Operations in Banking
Discover how a major financial institution automated its pentesting workflow to achieve continuous compliance and faster vulnerability remediation.

Continuous Resilience in Banking
CLIENT PROFILE
Tier-1 European Financial Institution
Banking | Fintech & Digital Payments | High-Compliance Critical Infrastructure
THE CHALLENGE
Securing a massive digital surface against evolving financial threats.
The entity faced the Herculean task of maintaining a robust security posture across thousands of subdomains, customer-facing applications, and legacy internal systems.
Traditional periodic pentesting was no longer sufficient. By the time a report was delivered, new vulnerabilities had already emerged, leaving a dangerous window of exposure.
Key considerations included:
-
Strict adherence to financial regulations (DORA/NIS2) regarding continuous monitoring.
-
High volume of assets making manual re-testing technically unfeasible.
-
Need for real-time visibility for stakeholders and forensic audit trails.
-
Integration of fragmented security findings into a single source of truth.
The structural problem was the disconnect between vulnerability discovery and the speed of technical remediation.
THE SOLUTION
Bridging the gap between discovery and defense with CAI.
CAI was deployed to transform a fragmented pentesting process into a streamlined, automated workflow. By integrating existing security tools and manual findings into the platform, the institution gained a centralized command center for its offensive security operations.
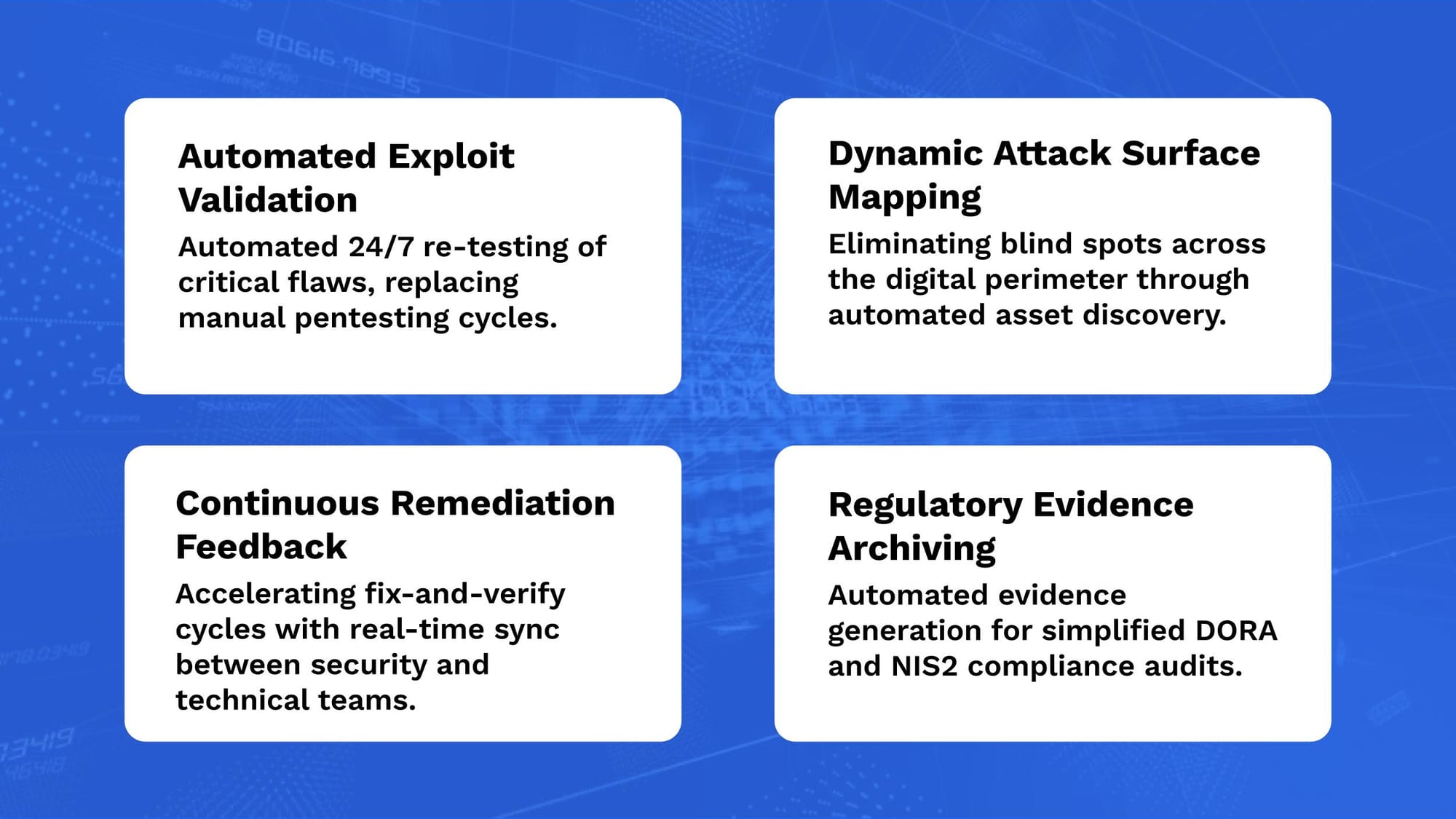
The platform was used to:
-
Automate validation of discovered vulnerabilities across the network.
-
Orchestrate continuous scanning of critical banking infrastructure.
-
Centralize assets and findings for cross-departmental visibility.
-
Generate audit-ready reports for regulatory compliance.
-
Prioritize remediation based on business impact and risk levels.
CAI acted as an automation layer within the security workflow
THE RESULTS
Measured efficiency in offensive operations.
IMPACT
From reactive testing to proactive risk management.
The implementation of CAI allowed the institution to move away from "snapshot" security toward a model of continuous assurance. By automating the repetitive tasks of pentesting, the internal security team was freed to focus on complex threat modeling and strategic defense, significantly increasing the cost of attack for potential adversaries.
CAI contributed as:
-
Centralized Security Hub.
-
Automation Engine for Validation.
-
Compliance Accelerator.
-
Risk Management Orchestrator.
This case demonstrates how organizations can maintain a high-frequency security cadence without proportional increases in manual overhead.
Want to explore how security automation can support your organization?
Get started with CAI.
Explore how these research insights translate into practical security with CAI — and join the conversation by following us on LinkedIn and X, or collaborating with the community on our Discord server.